UIC Zoom: Is Your Meeting REALLY Private? Find Out Now
In today’s interconnected world, video conferencing has become indispensable. Whether for work, education, or socializing, platforms like Zoom are the go-to choice. However, with convenience comes the crucial question of privacy. If you’re a user of the University of Illinois Chicago (UIC) Zoom platform, you’re likely wondering: How secure is my meeting? Is it really private? This article dives deep into the privacy features of UIC Zoom, helping you understand the tools at your disposal and how to ensure the confidentiality of your virtual gatherings.
Understanding the Privacy Landscape of Zoom
Zoom, like any platform, faces ongoing scrutiny regarding its security practices. While Zoom has implemented numerous improvements over the years, understanding the potential vulnerabilities and utilizing the available privacy settings is paramount. This is especially true for sensitive discussions or meetings where confidentiality is critical.
Key Privacy Features Offered by UIC Zoom
UIC provides its students, faculty, and staff with a licensed Zoom account, often with enhanced security features compared to free, personal accounts. Leveraging these features is the first step in protecting your meetings. Here’s a breakdown of the key privacy tools available:
- Password Protection: Requiring a password for your meetings is one of the most fundamental security measures. This prevents unauthorized access by individuals who haven’t received the password.
- Waiting Rooms: This feature acts as a virtual lobby. Participants must be admitted by the host before joining the meeting. This allows the host to vet attendees and prevent unwanted intrusions.
- Encryption: Zoom utilizes encryption to protect the data transmitted during your meetings. Look for end-to-end encryption options, which provide a higher level of security, especially for sensitive conversations.
- Host Controls: The host has significant control over the meeting. This includes:
- Muting participants
- Removing disruptive attendees
- Locking the meeting to prevent latecomers
- Disabling screen sharing for participants (unless authorized)
- Controlling recording capabilities.
- Authentication Profiles: UIC Zoom likely integrates with the university’s authentication system. This can restrict meeting access to only authorized UIC users, adding a layer of security.
- Reporting and Logging: Zoom allows hosts to report disruptive behavior and provides activity logs, which can be valuable for investigating potential security breaches.
Best Practices for Maximizing Privacy in Your UIC Zoom Meetings
Simply having the features doesn’t guarantee privacy. Proactive measures are crucial. Here’s a practical checklist for safeguarding your meetings:
- Always Use Passwords: Set a strong, unique password for every meeting, and communicate it securely (not via email).
- Enable the Waiting Room: This gives you control over who enters your meeting.
- Manage Screen Sharing: Only allow screen sharing for participants if necessary, and consider restricting it to the host only.
- Control Recording: Review the recording settings. You can choose who is allowed to record and whether you want to allow cloud recording or local recording. Always obtain consent before recording.
- Be Mindful of Shared Information: Avoid sharing sensitive data visually or verbally unless absolutely necessary.
- Keep Software Updated: Regularly update your Zoom client to benefit from the latest security patches and features.
- Secure Your Physical Environment: Ensure your physical surroundings are private and free from eavesdropping.
- Report Suspicious Activity: If you encounter any unusual behavior or suspect a security breach, report it immediately to the appropriate UIC IT support channels.
- Review UIC’s Specific Policies: Familiarize yourself with the university’s guidelines for using Zoom, including data privacy and security protocols.
Understanding Potential Vulnerabilities
While Zoom offers robust security, it’s essential to be aware of potential risks:
- Zoombombing: This is the unauthorized intrusion into a Zoom meeting, often by individuals who disrupt the meeting with offensive content. Following the best practices above significantly reduces this risk.
- Data Breaches: Zoom, like any platform, could be vulnerable to data breaches. Regularly reviewing your account settings and staying informed about potential security alerts is recommended.
- Malware: Clicking on suspicious links shared during a Zoom meeting can expose you to malware. Exercise caution and only click on links from trusted sources.
- Social Engineering: Phishing attempts, where attackers try to trick you into sharing your credentials, can compromise your account. Be wary of unsolicited emails or messages requesting your login information.
Conclusion: Taking Control of Your UIC Zoom Privacy
Using UIC Zoom doesn’t automatically guarantee complete privacy, but by understanding the available features, implementing best practices, and staying informed about potential vulnerabilities, you can significantly enhance the security of your meetings. Take control of your virtual environment and prioritize privacy to ensure a safe and productive experience. Regularly review your settings, stay informed about security updates, and always prioritize cautious behavior to minimize risks.
Frequently Asked Questions (FAQs)
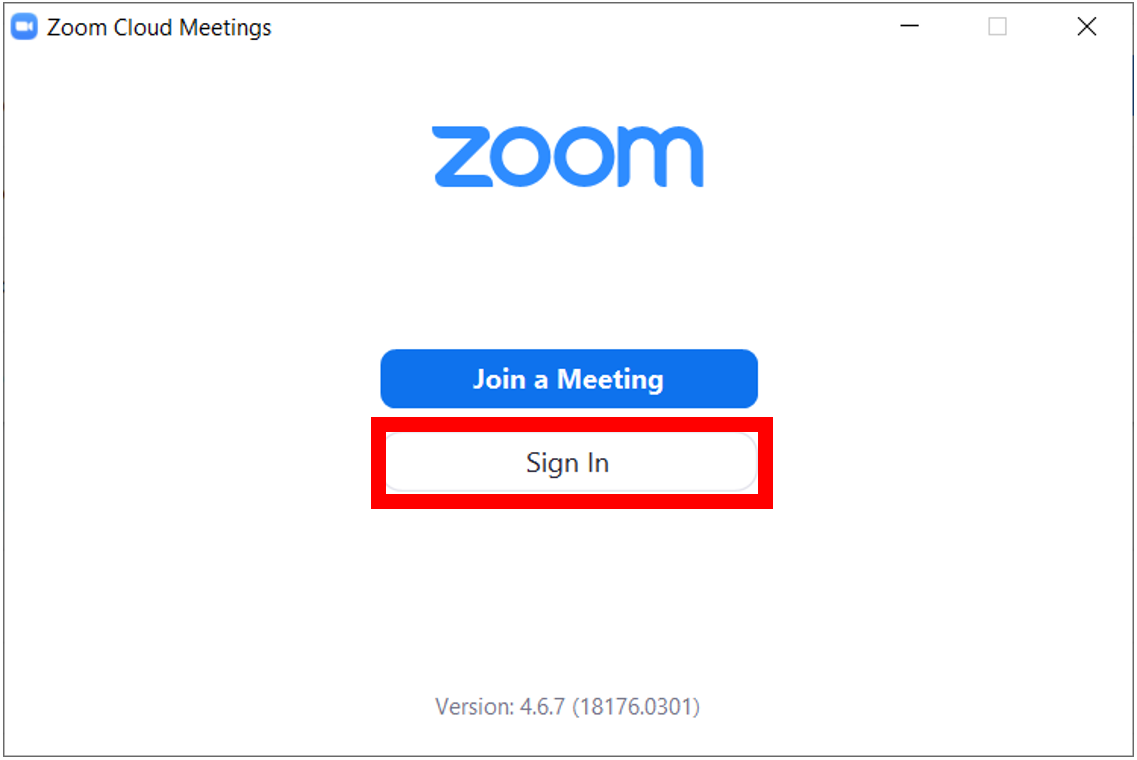
1. How do I enable a password for my UIC Zoom meeting?
When scheduling a meeting in the Zoom web portal or the Zoom client, there’s a setting to require a password. You’ll need to create a password and share it with your intended participants securely.
2. Where can I find the waiting room settings in my UIC Zoom account?
The waiting room setting is typically found in the meeting settings when scheduling or editing a meeting. You can also adjust the default settings in your Zoom account profile.
3. Are my Zoom recordings automatically encrypted?
Zoom offers different encryption levels. The specific encryption used for your recordings may depend on your account settings and the features available through UIC. Review your recording settings and consider enabling end-to-end encryption if you’re discussing sensitive information.
4. What should I do if I suspect someone has accessed my meeting without authorization?
Immediately end the meeting, report the incident to UIC IT support, and change your meeting password. Also, review your Zoom account settings for any unauthorized modifications.
5. Does UIC have specific guidelines for using Zoom?
Yes, UIC likely has specific policies regarding the use of Zoom, including data privacy and security protocols. Check the UIC IT website or contact their support for detailed information.